European Cybersecurity for the earliest stage of attacks.
Threat Intelligence Platform
Disrupt cyber attacks at reconnaissance and mass exploitation stages. Advanced fingerprinting, automated blocklists, and real-time threat feeds.
No credit card required
Latest product updates & research

Sanctioned, Seized, Still Scanning: Inside a Russian Bulletproof Hosting Network Targeting the EU
On 18 May 2026, Dutch investigators seized more than 800 servers and broke up a hosting operation that prosecutors say powered Russian cyberattacks across the EU. We had spent the previous year watching the same network from the other side. After the seizure, the scanning did not stop.

New Integrations for Microsoft Sentinel and MISP
ELLIO is expanding its threat intelligence ecosystem with two new integrations designed for SOC, detection engineering, and threat intelligence workflows: Microsoft Sentinel via TAXII 2.1 and a native MISP integration.
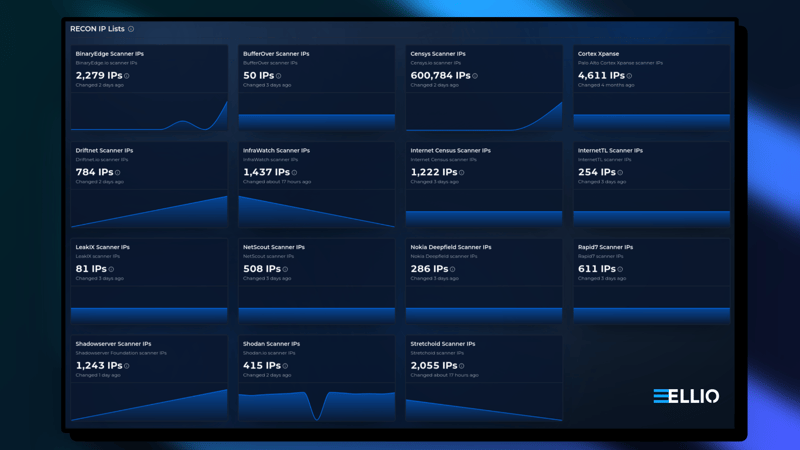
ELLIO expands with 10 new recon and scanner IP feeds
ELLIO Threat Intelligence & Blocklist Automation has been updated with 10 new scanner and recon IP address feeds. This improves detection and control of scanning activity at the network perimeter, enabling more accurate allow and block rules without manual IP range management.
Stories from ELLIO
Microsoft Security Naming Survival Guide
A quick guide to Microsoft security name changes, helping you make sense of current terms without getting lost in older names.

Why Microsoft Sentinel Feels Noisy: It’s Not Volume, It’s Recon Blindness
Alert fatigue in Microsoft Sentinel is not caused by alert volume alone. It is a context and correlation problem. Read how reconnaissance-aware threat intelligence helps separate internet scanning noise from active exploitation activity to improve signal quality and reduce false-positive incidents.

Threat Intelligence Platforms by Use Case: 2026 Guide
Not all CTI platforms are built for the same purpose. Differences in data sourcing, architecture, and enrichment capabilities mean the “best” platform is defined by its fit for operational use cases, such as reducing SIEM noise, supporting threat hunting, or detecting fraud.
What We Build
Learn more about each product on ellio.tech
ELLIO Threat Intelligence
Access clean, high-fidelity threat data focused on mass exploitation and reconnaissance, turning raw signals into context-rich insights your security stack can act on instantly - from SIEM, SOAR, TIP to firewalls.
ELLIO Blocklist Automation
Manage all your blocklists and IP rules from a central place. Define what’s allowed and what’s blocked – broadly or with fine granularity. Apply rules automatically across all your firewalls.
ELLIO IP Blocklists
Dynamic, context-driven threat lists. Updated automatically every 5 minutes or as needed.
ELLIO Recon IP Lists
Continuously updated lists of scanner IPs. Define exactly which scanners to block or always allow.
ELLIO rDNS Dataset
Complete IPv4 reverse DNS. ~1.25 billion clean PTR records, updated daily.
ELLIO Fingerprint Firewall
Unifies network fingerprints, user-provided signatures, and traditional IP blocklists into a single, actionable defense layer.