Coordinated Credential-Stuffing Campaign Targets Palo Alto GlobalProtect Portals
A coordinated credential-stuffing campaign hit GlobalProtect VPN portals with 8,575 IPs in 48 hours. Three attack waves, 78 targeted usernames, one password. Our team breaks down the timeline, infrastructure, fingerprints, and what defenders can do.
.png)
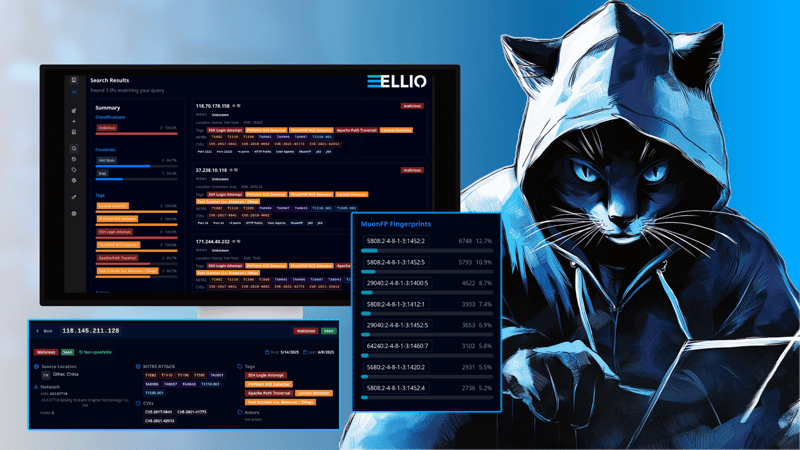
On February 23, 2026, ELLIO's global deception network recorded an 11x spike in scanning activity targeting Palo Alto GlobalProtect VPN portals (/global-protect/login.esp). Over the following 48 hours, the campaign delivered approximately 30,000 sessions from 8,575 unique source IPs in three distinct waves, combining reconnaissance probing with credential-stuffing attempts using a fixed set of 78 employee-style usernames and a single password.
This is not the first campaign of its kind. Each wave follows a similar playbook but rotates to fresh hosting infrastructure. This wave introduced GTT Communications (AS3257) as the primary carrier.
Timeline
The campaign baseline for /global-protect/login.esp scanning averaged 627 unique IPs per day across the preceding 34 days (January 20 - February 22). On February 23, that number jumped to 6,726.
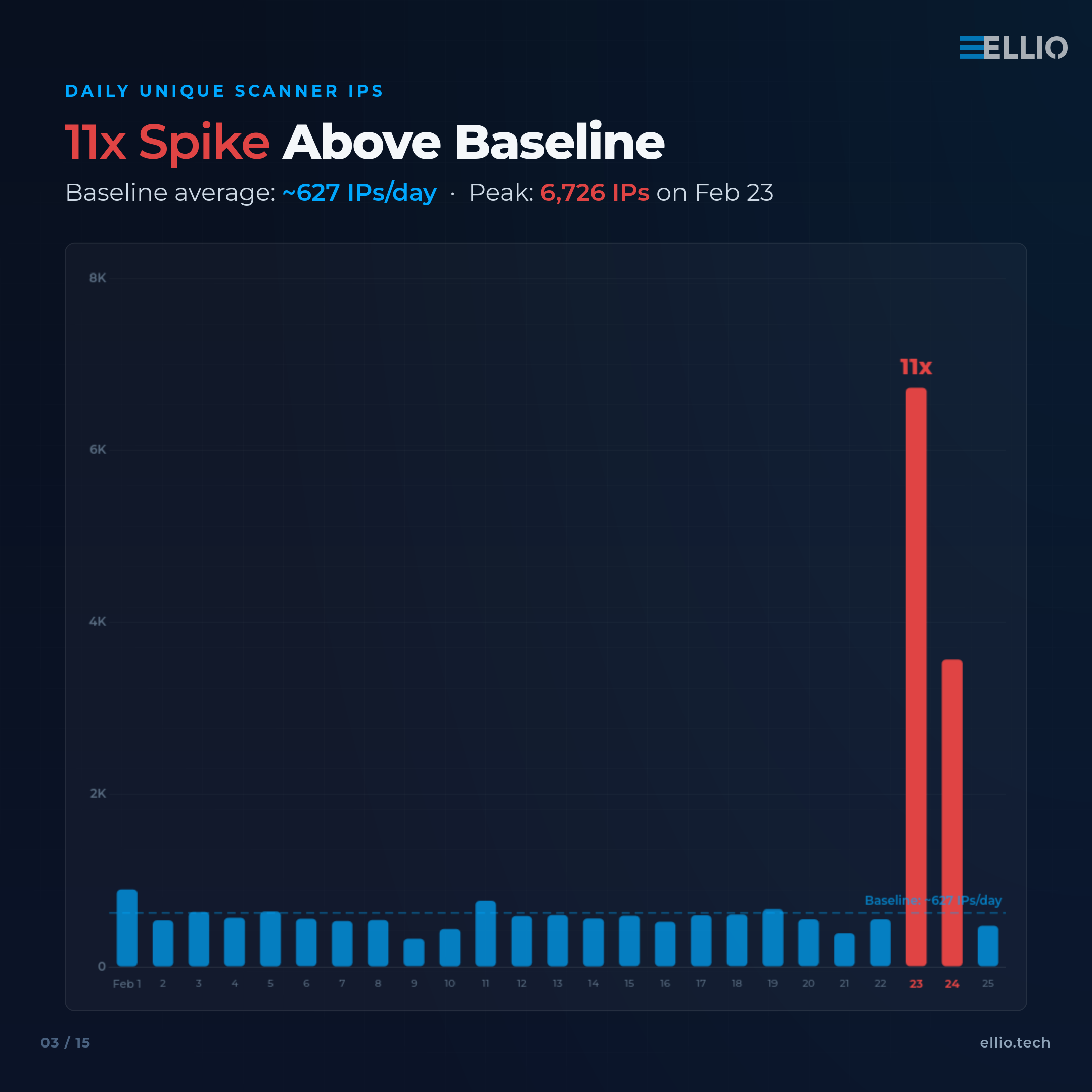
ELLIO's deception network reveals three distinct bursts:
┌────────┬─────────────────────┬──────────┬────────────┬────────────┐
│ Wave │ Time (UTC) │ Sessions │ Unique IPs │ Methods │
├────────┼─────────────────────┼──────────┼────────────┼────────────┤
│ Wave 1 │ Feb 23, 09:00-11:00 │ 9,084 │ 3,820 │ GET + POST │
├────────┼─────────────────────┼──────────┼────────────┼────────────┤
│ Wave 2 │ Feb 23, 17:00-20:00 │ 12,640 │ 5,902 │ GET + POST │
├────────┼─────────────────────┼──────────┼────────────┼────────────┤
│ Wave 3 │ Feb 24, 08:00-12:00 │ 6,036 │ 3,176 │ GET only │
└────────┴─────────────────────┴──────────┴────────────┴────────────┘
Between waves, traffic dropped to baseline levels (20 - 50 sessions/hour), indicating deliberate orchestration rather than continuous scanning.
Attack Pattern
The campaign followed a consistent two-phase approach.

Phase 1 - Reconnaissance
GET requests to /global-protect/login.esp probed for the presence of live GlobalProtect portals. These accounted for ~89% total sessions.
The requests used HTTP/1.0 with a Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.0.0 Safari/537.36 User-Agent string and a Referer: https://www.google.com header.
Phase 2 - Credential Stuffing
A subset of IPs followed up with POST requests submitting authentication payloads in the following format:
prot=http&server=<target_ip>:<port>&inputStr=&ok=Log+In&action=getsoftware&user=<username>&passwd=Password1
3,061 POST sessions originated from 2,193 unique IPs. All attempts used the same single password ("Password1") across a fixed dictionary of 78 usernames in first_initial + last_name format (e.g., acobb, jholt, tgraves).
The uniform password and structured username list suggest this phase may function more as aggressive reconnaissance - testing which portals accept the authentication form and respond - rather than a serious exploitation attempt.

POST activity was limited to Waves 1 and 2 on February 23. Wave 3 on February 24 consisted entirely of GET requests.
Infrastructure
GTT Communications (AS3257) carried 93.2% of the campaign's sessions (27,313 of 29,311), sourced from two primary IP blocks:
┌──────────────────┬──────────┐
│ Block │ Attempts │
├──────────────────┼──────────┤
│ 154.208.64.0/18 │ 18,369 │
├──────────────────┼──────────┤
│ 154.206.240.0/20 │ 8,941 │
└──────────────────┴──────────┘

An additional 29 ASNs contributed the remaining 6.8% of traffic:
┌──────────┬────────────────────┬──────────┬────────────┐
│ ASN │ Name │ Requests │ Unique IPs │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS202425 │ IP Volume Inc │ 526 │ 5 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS132203 │ Tencent Cloud │ 342 │ 221 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS396982 │ Google LLC │ 138 │ 112 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS14061 │ DigitalOcean │ 110 │ 72 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS398324 │ Censys, Inc. │ 103 │ 81 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS16509 │ Amazon.com │ 92 │ 28 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS6939 │ Hurricane Electric │ 82 │ 74 │
├──────────┼────────────────────┼──────────┼────────────┤
│ AS213438 │ ColocaTel Inc. │ 19 │ 4 │
└──────────┴────────────────────┴──────────┴────────────┘Of all contributing ASNs, only one non-GTT source (ColocaTel Inc., 4 IPs) attempted POST requests. The remaining non-GTT traffic consisted entirely of GET reconnaissance.
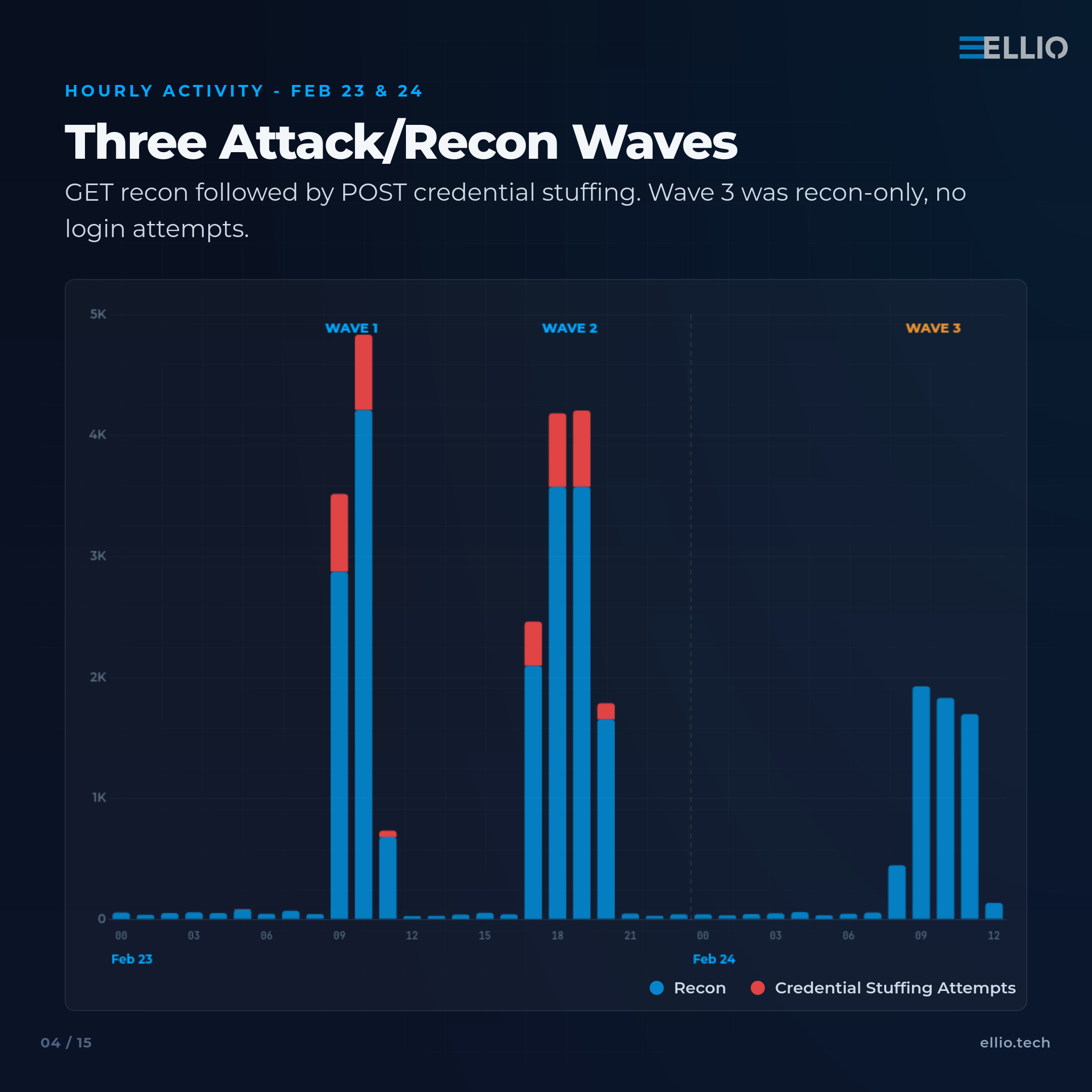
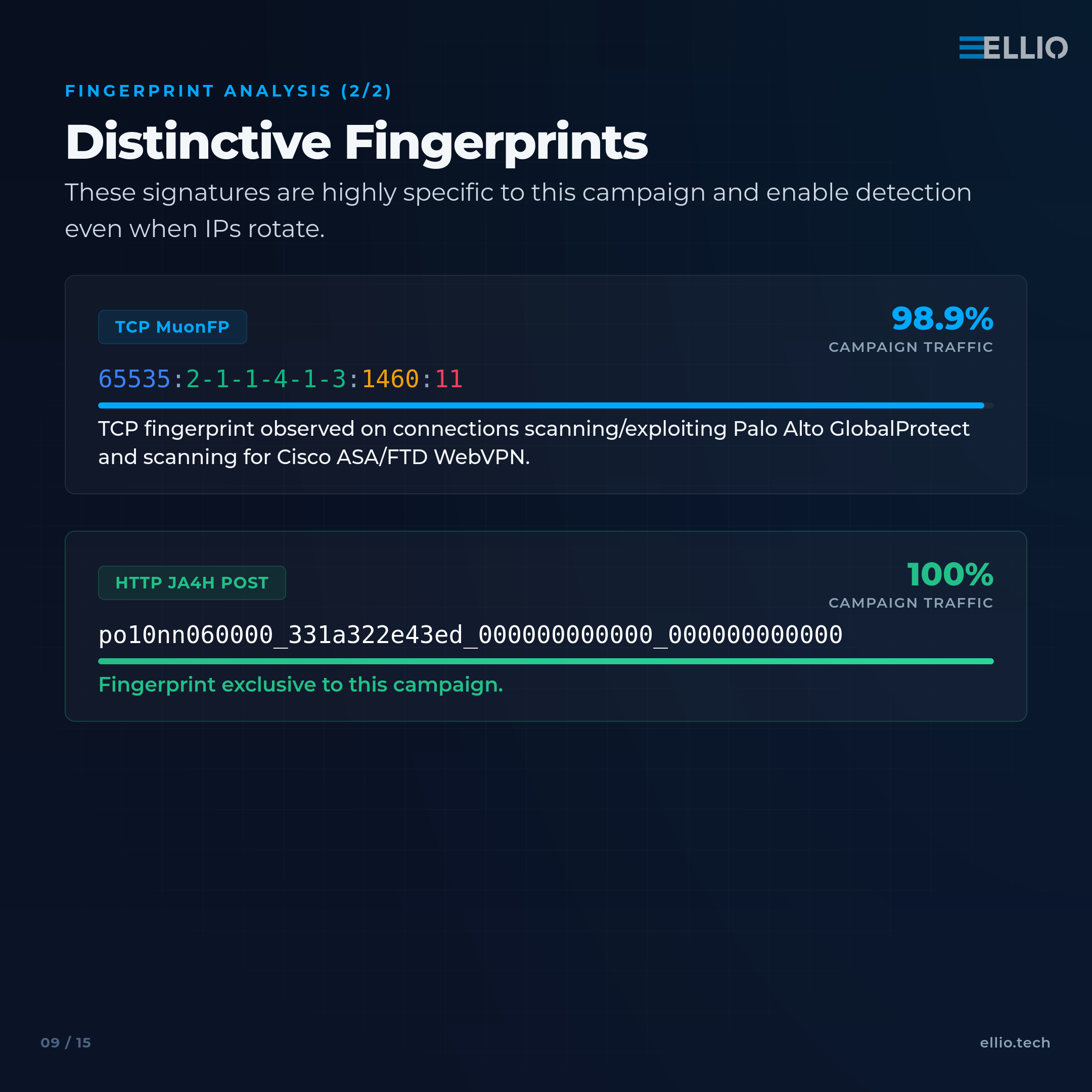
Fingerprint Analysis
Our team correlated the campaign's network fingerprints against our full database to assess how useful each one is as a detection signal. Not all fingerprints are created equal - some are shared across half the internet, while others pinpoint a specific tool or campaign with high confidence.
┌─────────────────────────────────────────────────────┬────────────┬─────────────┬─────────────────────────────────────────────────────────────────────────┐
│ Fingerprint │ Type │ Campaign │ Assessment │
│ │ │ IPs │ │
├─────────────────────────────────────────────────────┼────────────┼─────────────┼─────────────────────────────────────────────────────────────────────────┤
│ 65535:2-1-1-4-1-3:1460:11 │ MuonFP │ ~4,052 │ Highly distinctive TCP fingerprint. Predominantly malicious. │
│ │ (TCP) │ │ │
├─────────────────────────────────────────────────────┼────────────┼─────────────┼─────────────────────────────────────────────────────────────────────────┤
│ po10nn060000_331a322e43ed_000000000000_000000000000 │ JA4H │ 1,818 │ Fingerprint exclusive to this campaign. │
│ │ (POST) │ │ │
├─────────────────────────────────────────────────────┼────────────┼─────────────┼─────────────────────────────────────────────────────────────────────────┤
│ ge10nr040000_532a1ee47909_000000000000_000000000000 │ JA4H (GET) │ 7,328 │ Nearly exclusive to this campaign (99.7%). │
├─────────────────────────────────────────────────────┼────────────┼─────────────┼─────────────────────────────────────────────────────────────────────────┤
│ ca39305c183742559eb9946bcb9dc220 │ JA3 │ 7,504 │ 3rd most common JA3 globally. Shared with other scanners, not │
│ │ │ │ distinctive on its own. │
├─────────────────────────────────────────────────────┼────────────┼─────────────┼─────────────────────────────────────────────────────────────────────────┤
│ t12i280800_0df5e5c63df4_686390af6b8e │ JA4 │ 7,514 │ Overlaps with JA3 population. Common, not distinctive alone. │
└─────────────────────────────────────────────────────┴────────────┴─────────────┴─────────────────────────────────────────────────────────────────────────┘The MuonFP value flags infrastructure that is predominantly associated with malicious scanning activity. The JA4H POST fingerprint is the most precise indicator, appearing on only one IP outside the campaign globally. Together, these fingerprints provide reliable detection of the campaign's tooling regardless of IP rotation.
For more on combining IP and fingerprint-based blocking, see: "IP Blocking vs TCP Fingerprint Blocking: How to use and combine them".
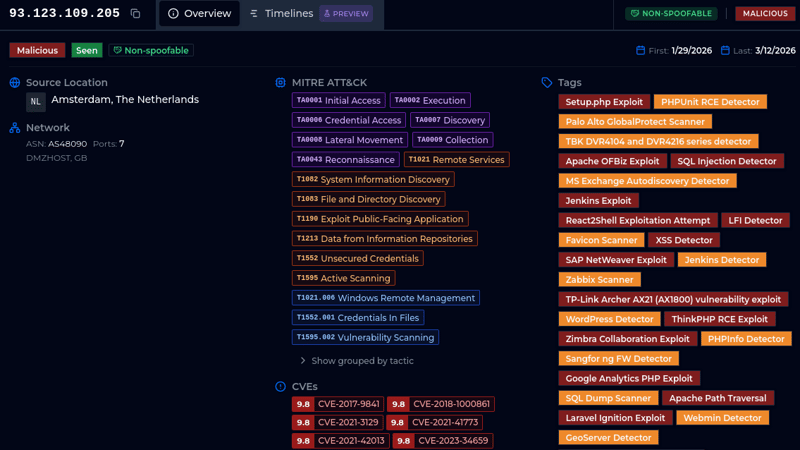
Track This Campaign
You can track this campaign directly on the ELLIO platform using the following queries:
All GlobalProtect reconnaissance activity: tag: "Palo Alto GlobalProtect Scanner"
Exploitation attempts, including credential stuffing: tag: "Palo Alto GlobalProtect Exploit"
Narrow to the primary campaign infrastructure: tag: "Palo Alto GlobalProtect Exploit" AND src.asn.number: "3257"
These queries are live in ELLIO Threat Platform and will continue to surface new IPs as they appear on our sensors - including future waves that may use entirely different infrastructure.
Defensive Takeaways
Recon precedes exploitation - automated blocklists exploit that gap.
In this campaign, GET probing preceded credential stuffing by hours within each wave.
Organizations subscribed to dynamically updated threat feeds had these IPs blocked before the first POST request fired. Those who blocked reconnaissance traffic at the perimeter were effectively invisible to the campaign's second phase entirely.
Stack Your Defenses.
IP blocklists catch known bad actors. TCP and HTTP fingerprint blocking catches the tools they use, even when they rotate to fresh IPs. Layering both disrupts reconnaissance and exploitation simultaneously.
VPN portals remain high-value targets.
GlobalProtect, along with other VPN and security appliance portals, continues to attract recurring credential-stuffing campaigns. The hosting infrastructure changes, but the playbook does not.
Indicators of Compromise
Target path: /global-protect/login.esp
Password used across all attempts: Password1
78 usernames:
┌──────────┬───────────┬──────────┬───────────┬───────────┬───────────┐
│ acobb │ aconner │ afloyd │ ahaynes │ ahorton │ amcdaniel │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ amcguire │ amoody │ apark │ aschwartz │ asparks │ athornton │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ atyler │ awarner │ awolfe │ bbenson │ bholt │ bschwartz │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ bvazquez │ cholt │ cneal │ cpark │ cterry │ cvaughn │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ dbush │ dgraves │ dholt │ dmiles │ dpadilla │ dpark │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ dsteele │ dvaughn │ ebush │ egraves │ epark │ esteele │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ jbenson │ jholt │ jpark │ jparks │ jterry │ jvaughn │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ khaynes │ kmiles │ kneal │ kpark │ kvaughn │ lgraves │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ lnavarro │ lpark │ lvaughn │ mhale │ mholt │ mneal │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ mpark │ mschwartz │ mterry │ mwarner │ rgraves │ rhale │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ rmiles │ rneal │ rpadilla │ rpark │ sbenson │ shale │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ sneal │ sschwartz │ ssteele │ sterry │ svazquez │ tbenson │
├──────────┼───────────┼──────────┼───────────┼───────────┼───────────┤
│ tbush │ tgraves │ thale │ tholt │ tschwartz │ tvaughn │
└──────────┴───────────┴──────────┴───────────┴───────────┴───────────┘Primary IP blocks:
┌──────────────────┬─────────────────────────────┐
│ Block │ ASN │
├──────────────────┼─────────────────────────────┤
│ 154.208.64.0/18 │ AS3257 (GTT Communications) │
├──────────────────┼─────────────────────────────┤
│ 154.206.240.0/20 │ AS3257 (GTT Communications) │
└──────────────────┴─────────────────────────────┘The full list of source IPs is available in ELLIO Threat Platform and in ELLIO Threat List MAX (as of the time of the campaign).