Analyze everything or move straight to network-level blocking?
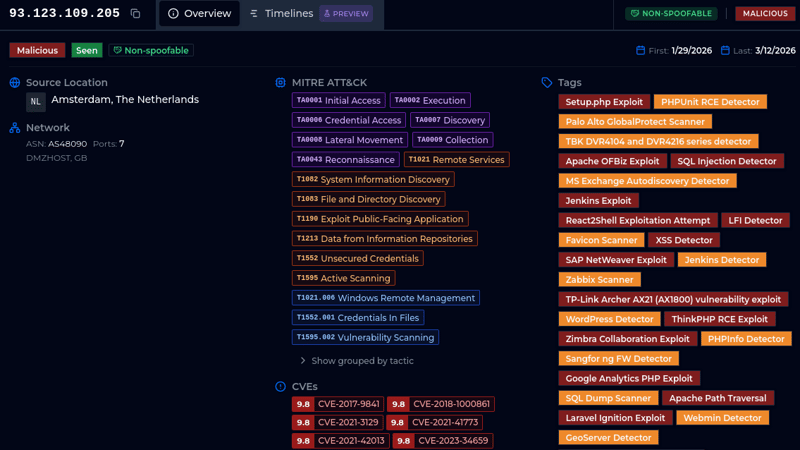
One IP. Four days. Nearly 900 user agents. Over 3,000 probes. Sometimes a single IP address tells you everything you need to know about how industrialized internet scanning has become.
5 articles tagged with "Network Fingerprints"
One IP. Four days. Nearly 900 user agents. Over 3,000 probes. Sometimes a single IP address tells you everything you need to know about how industrialized internet scanning has become.
.png)
A coordinated credential-stuffing campaign hit GlobalProtect VPN portals with 8,575 IPs in 48 hours. Three attack waves, 78 targeted usernames, one password. Our team breaks down the timeline, infrastructure, fingerprints, and what defenders can do.
The journey began in 1969, when the very first RFC - Request for Comments - was published. Explore key milestones that shaped network security and the practice of network fingerprinting.
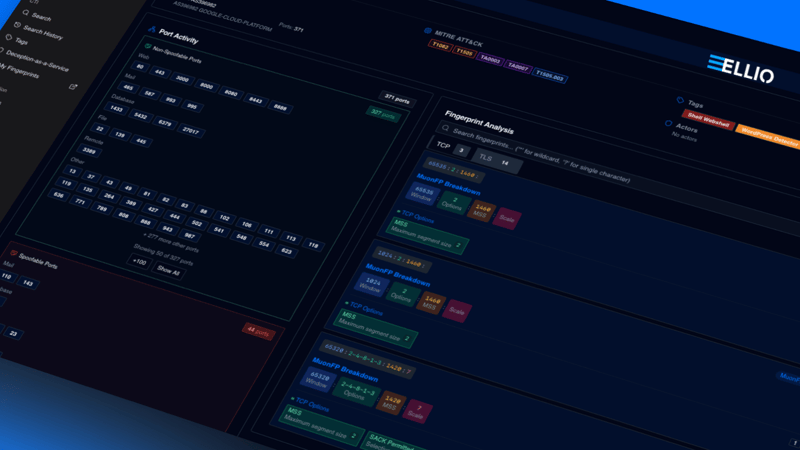
Learn practical tips for deploying JA4, JA3, and MuonFP fingerprints in your security operations. Get expert insights from Vlad Iliushin and discover how to unlock their full defensive value.

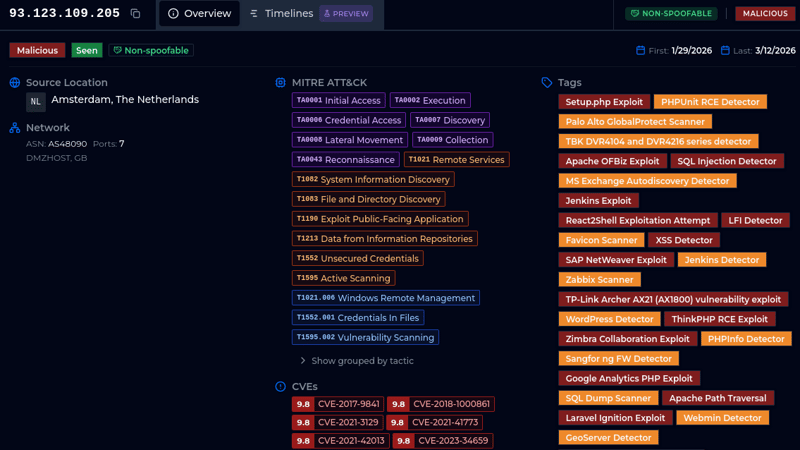
Learn how combining Threat Intelligence-based IP blocking and TCP fingerprinting enhances network security by disrupting attacker reconnaissance.