"n8n" is the new "admin."
On February 10, 2026, our deception network recorded "n8n" overtaking "admin" as the #2 most brute-forced SSH username. The campaign scaled from a handful of probing IPs to hundreds of unique sources in under a week, with attackers rapidly iterating through password variants.
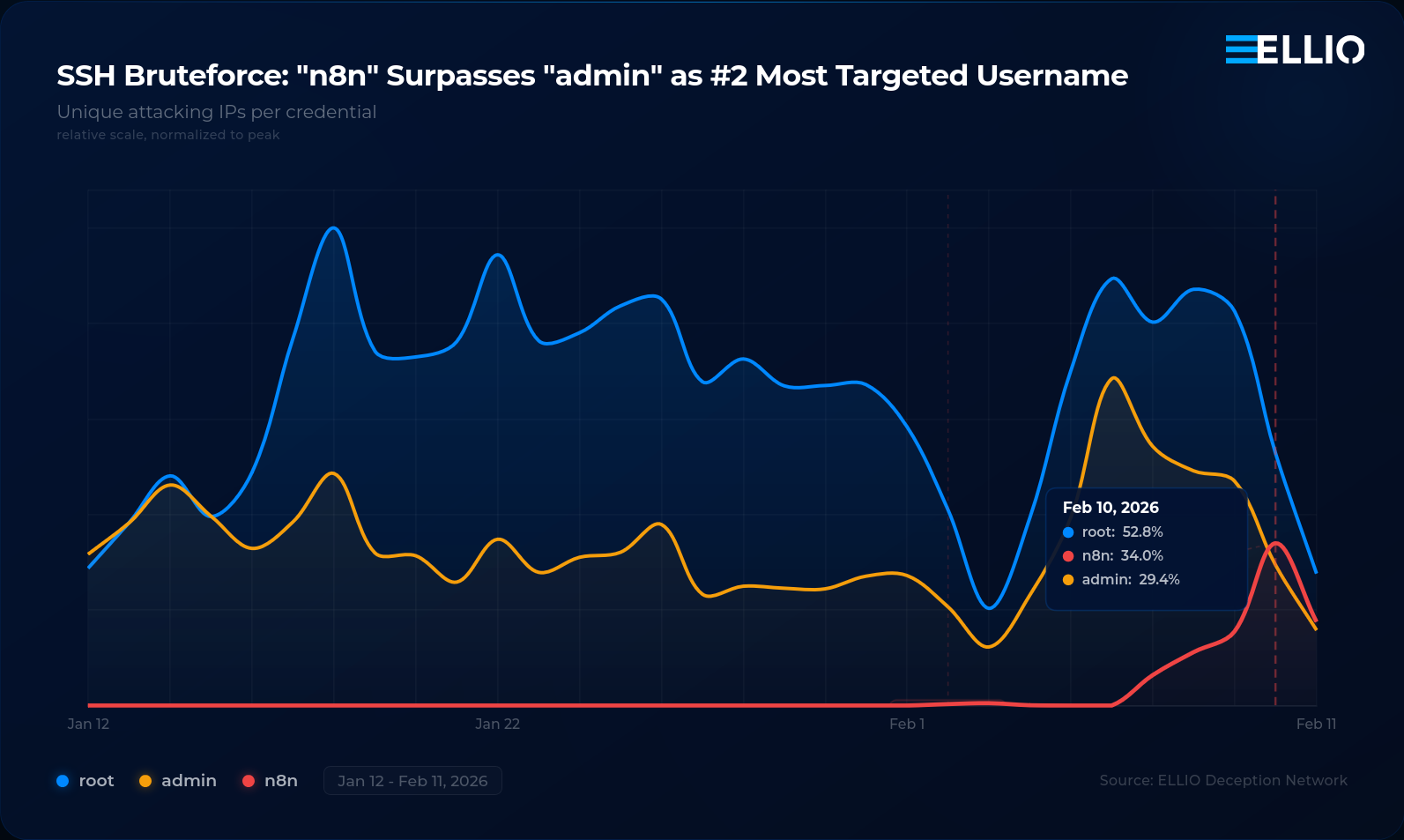
For years, the two most brute-forced SSH usernames have been the same: root and admin.
Boring, I know.
That changed yesterday, on February 10. Our deception network recorded n8n overtaking admin as the #2 most targeted SSH username on the internet. A workflow automation tool now gets more brute-force attention than one of the most generic default credentials in computing history.
And it happened in 11 days flat.
Here is the timeline:
- Beginning of February -
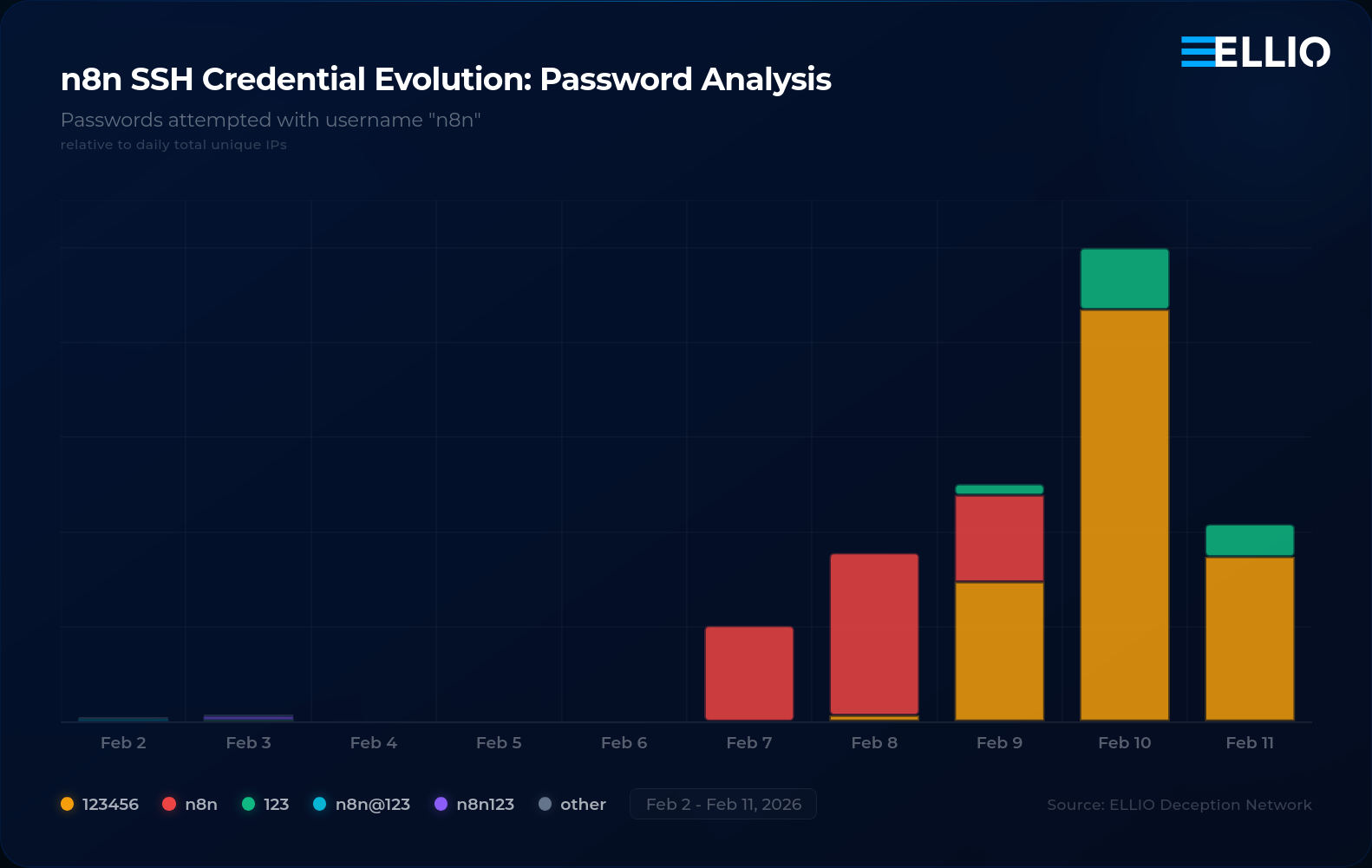
n8nusername appears. A handful of IPs, targeted passwords from wordlists liken8n@123andn8n123!. - Feb 7 - Botnet kicks in. Automated tools try
n8n:n8n. - Feb 9 - Operators iterate.
n8n:123456replacesn8n:n8nas the top credential. - Feb 10 - Full scale. Hundreds of unique IPs scanning for n8n.
admindrops to #3.
The username/password evolution tells the real story. Attackers started with product-specific guesses, pivoted to the obvious default, then settled on the thing that works. A botnet operator testing,
learning, and optimizing their wordlist in near real time.
Why n8n? Self-hosted workflow automation has exploded. If you follow the n8n setup guide, it does not specify which system username to use - but it is not a long stretch to use "n8n" for an
n8n service. Just like we did for 20 services before, and like we will do for 20 services after. Attackers watch adoption curves just as closely as VCs do - and the moment a platform gains
traction, it gets added to the wordlist.
Will it stay at #2?
Spoiler alert - it won't.
These campaigns come in waves. But the signal matters more than the ranking: attackers are actively tracking which self-hosted platforms are gaining adoption and updating their wordlists accordingly.
And here is the part that should make you think twice. Most n8n instances are not just running simple automations anymore. They are wired into OpenAI, Anthropic, cloud APIs - loaded with tokens and credentials for AI models. A compromised n8n instance is not just a foothold into a network. It is a ready-made automation platform with API keys to burn.
How long until someone builds the first AI SDR botnet off the back of stolen n8n workflows? Your compromised automation pipeline, their outbound campaign at scale.
Advisory If you are self-hosting n8n:
- Disable SSH password authentication. Keys only.
- Never expose SSH directly to the internet.
- Deploy behind a reverse proxy with proper access controls.
- Idk, throw ELLIO dynamic blocking to ease your access logs from all RECON and mass exploitation.
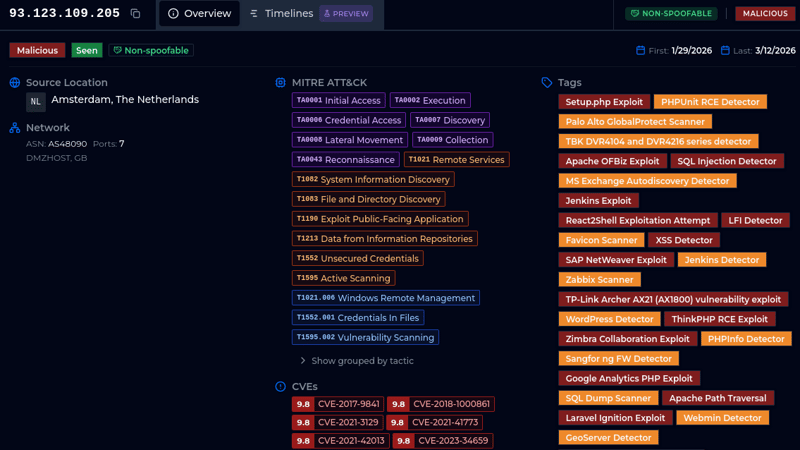
The scanning infrastructure spans DigitalOcean, OVH, UCloud HK, Microsoft Azure, and Indonesian cloud providers. The usual VPS-based botnet footprint.admin had a good run. It will be back. But for one day, n8n took the crown.

.png)